DATA LAKE GOVERNANCE
- Home >
- Platform >
- Open Data Lake Platform >
- Data Lake Governance >
- Security
Data protection, secure access with encryption, and RBAC controls. Leverage leading cloud provider IAMs, AD, and LDAP implementations to provide the same rights and privileges to access the data.
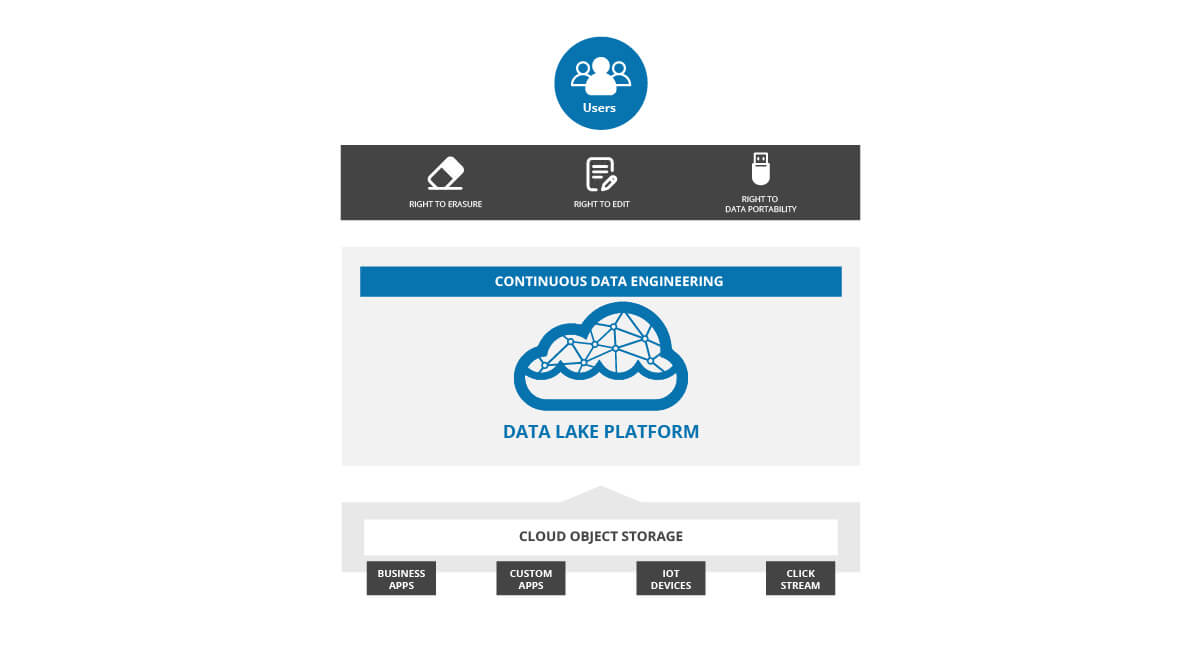
Cloud Data Lake Governance
Efficient updates and deletes for data stored in cloud data lakes to comply with regulations for the right to forget and the right to erase.
Native support for ACID transactions across multiple engines to avoid lost updates, dirty reads, stale reads and enforce application-specific integrity constraints.
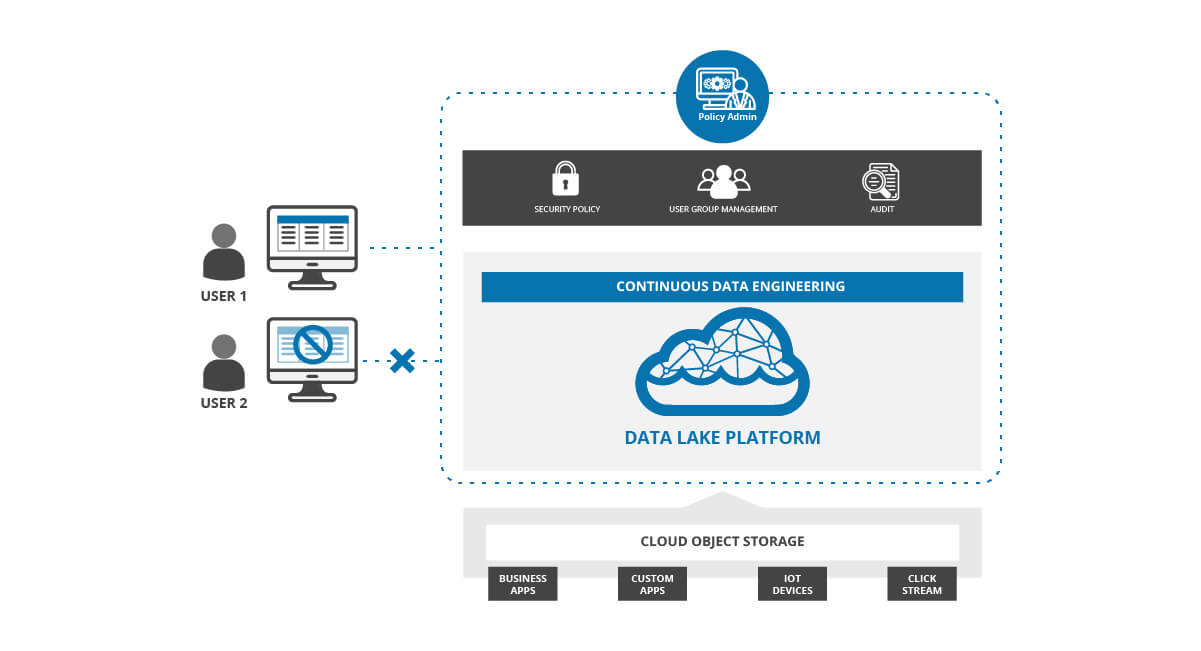
Cloud Data Lake Security
Provides granular data access controls and the ability to mask data with a single policy across multiple engines.
Anonymize data based on row and column filtering.
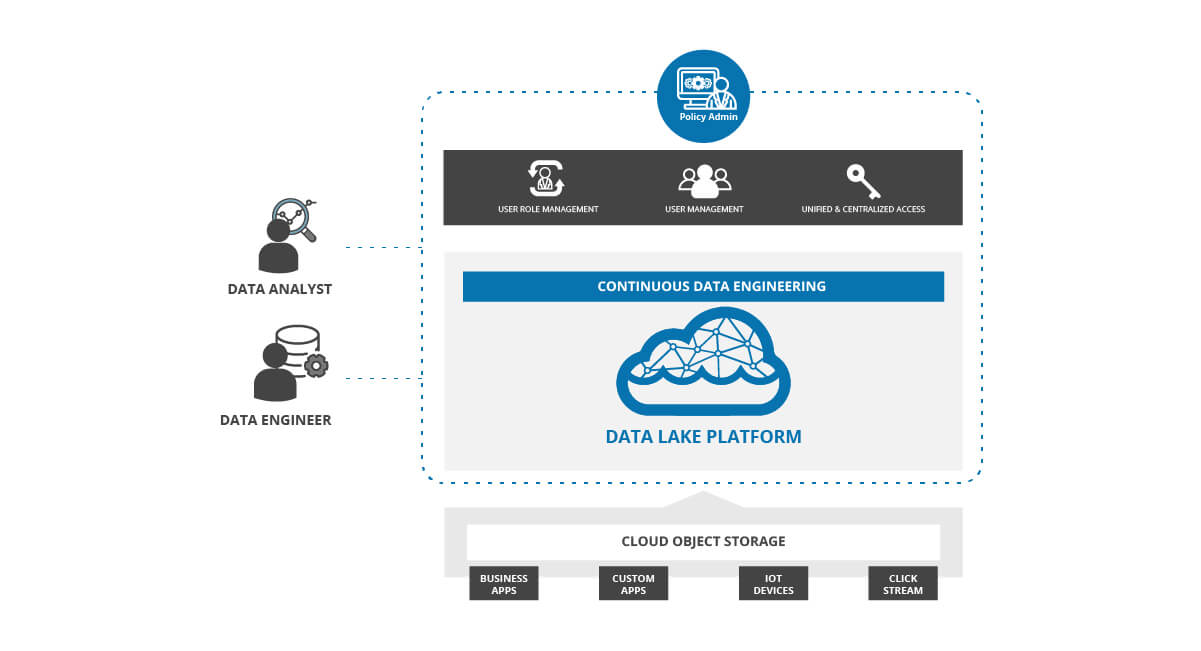
Role-Based Access Control
Enable access controls at a minimum of three levels for effective policy management:
1. Data ingest and data access
2. Infrastructure and platform
3. Data levels
Leverage your cloud provider’s IAM/AD/LDAP services to restrict particular user access to resources.
SECURITY
Visit trust.qubole.com to learn more about Qubole Trust, Security and Compliance policy


